Federal Court imposes AUD 2.5 million fine for breach of AFSL obligations
In brief
The Federal Court of Australia in Australian Securities and Investments Commission v FIIG Securities Limited [2026] FCA 92 has ordered FIIG Securities Limited (FIIG) to pay a penalty of AUD 2.5 million plus AUD 500,000 in costs in response to proceedings brought by the Australian Securities and Investment Commission (ASIC) in March 2025 for cyber security failures in breach of FIIG’s general Australian Financial Services Licence (AFSL) obligations between March 2019 and June 2023.
FIIG’s cyber security failures were found to have culminated in approximately 385GB of data being compromised in a cyber-attack beginning 19 May 2023, affecting approximately 18,000 FIIG clients.
This case marks the first time the Federal Court has imposed civil penalties for cyber security failures under the general AFSL obligations and highlights ASIC’s increased focus on cyber risk management and its “clear license-to-operate expectation for robust resilience”.
Key takeaways
Cyber security and cyber resilience are essential elements of an AFSL holder’s obligations. This case highlights that:
- ASIC has prescriptive and technical expectations for risk management systems and cyber security controls and is likely to take a detailed forensic approach to evaluate whether an AFSL holder’s risk management systems and cyber security controls are adequate and proportionate to its data sensitivity, scale and business risks, particularly in the wake of a cyber-attack that results in disclosure of client data;
- Businesses with an AFSL need to ensure that their risk management systems and cyber security measures adequately address cyber security risk, including by deploying adequate financial, technological and human resources to ensure adequate cyber security measures are in place;
- Failure to do so can result in non-compliance with AFSL obligations, ASIC proceedings and penalties;
- Adequate cyber security measures need to be proportionate to the nature of the business, extent and complexity of information held, the value of assets held, the magnitude and potential consequences of the cyber security risks and any contractual obligations the ASFL holder has to its clients; and
- Employees with responsibility for ensuring adequate cyber security measures are in place must be appropriately experienced and given sufficient time and resources to properly discharge their responsibilities.
In depth
Background
FIIG is an Australian fixed-income specialist and AFSL holder and is subject to various obligations under the Corporations Act 2001 (Cth) (“Act”) including the general AFSL obligations under section 912A(1) of Act. In providing financial services, FIIG collects and maintains extensive and detailed personal information about its clients. At the time of non-compliance, FIIG held between approximately AUD 2.99 – 3.7 billion in client assets under management. Given these factors, ASIC alleged that there was a real and foreseeable risk that FIIG would be the subject of an attempted or actual cyber-attack, yet failed to implement adequate controls. A cyber-attack in fact occurred from 19 March 2023 to 8 June 2023 and resulted in the theft and subsequent release of sensitive client data onto the dark web. FIIG was unaware of the event until the Australian Cyber Security Centre (ACSC) alerted FIIG on 2 June 2023.
ASIC’s cyber security and resilience expectations to meet general AFSL obligations
The proceedings illustrate ASIC’s detailed, technical and prescriptive expectations for risk management systems and cyber security controls (including vulnerability scanning and threat detection) and appropriate resourcing (including human resources) to meet general AFSL obligations under the Act, including to:
- Ensure financial services are provided efficiently, honestly and fairly (section 912A(1)(a));
- Have available adequate resources (including financial, technological and human resources) to provide the relevant financial services (section 912A(1)(d)); and
- Have adequate risk management systems (section 912A(1)(h)).
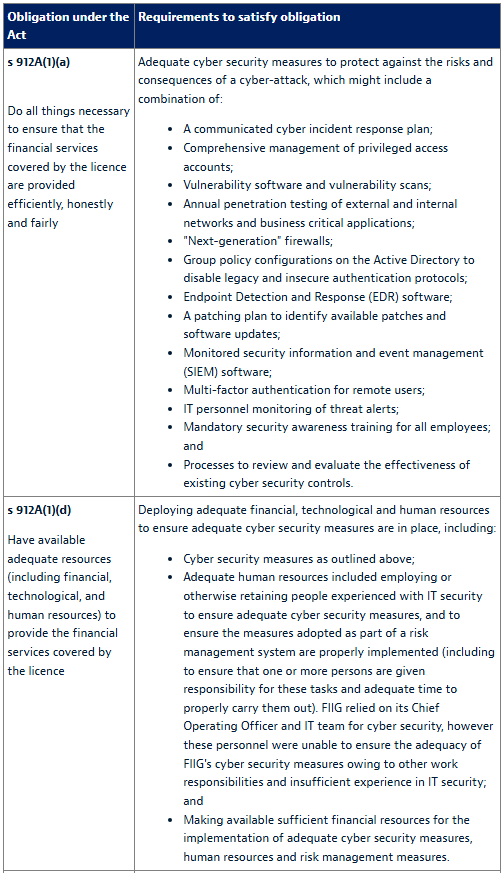
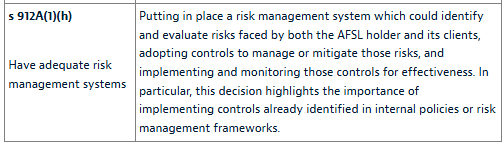
The table below summarises ASIC’s expectations coming out of this decision in relation to the risk management systems and controls that would have enabled FIIG to meet its general AFSL obligations under section 912A(1)(a), (d) and (h) of the Act and provides a useful point of reference for other AFSL holders (taking into consideration the relative nature of their business, extent and complexity of information held and the value of assets held).
Looking ahead: ASIC’s ongoing focus on cyber security enforcement
ASIC’s 2026 key issues outlook identifies cyber-attacks, data breaches and inadequate operational resilience and crisis management as harmful threats to market confidence and consumers that it will continue to focus on.
Regulators like ASIC will consider not just whether AFSL holders have risk management frameworks in place, but whether they are:
- Properly and consistently implemented by way of effective controls;
- Proportionate to nature of the business, sensitivity and extent of information and the value of assets held;
- Tested and reviewed on a regular basis;
- Adequately supported by personnel and financial resources; and
- Subject to appropriate governance and oversight.
In this environment it is particularly important for ASIC-regulated businesses and AFSL holders to ensure that cyber resilience is embedded into their licence compliance and governance frameworks, to be able to demonstrate that they have strong risk management measures in place and to test the robustness of these measures regularly and address any identified vulnerabilities to mitigate against the risk of a cyber-attack or data breach.
* * * * *
Vanessa Franco, Summer Clerk, has contributed to this legal update.







